Remote and hybrid work has become normal in recent years.
It’s well established that these working policies help employees achieve a better work-life balance. They also help employers secure the best talent—even if it’s not local to a...
I’m excited to announce that Parallels® RAS (Remote Application Server) has been awarded the prestigious TrustRadius Buyer’s Choice Award!
This honor celebrates our dedication to delivering world-class solutions...
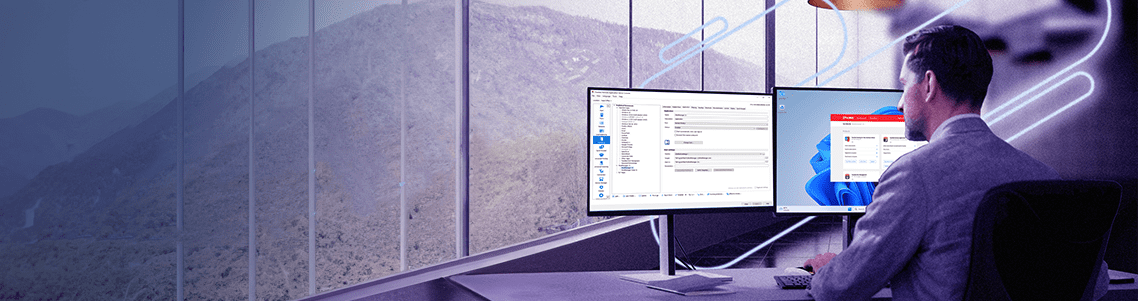
The latest release of Parallels RAS, version 20, introduces exciting new features and enhancements that elevate the admin and end-user experience with increased flexibility, security, and...
The future is in the cloud, and the Business Intelligence Group is shining a spotlight on the companies, products, and individuals shaping this transformative landscape and driving it...
In Desktop-as-a-Service (DaaS) space, Parallels has not just established itself, but it’s rising with its innovative approach.
In the latest Gartner Magic Quadrant...
Earlier this year, we announced Parallels DaaS, a solution to simplify IT management by centralizing the deployment, management, and maintenance of virtual desktops and applications.
This...
We are thrilled to announce that Parallels DaaS, a product instrumental in shaping the IT channel community, has been honored with the prestigious CRN Technology Innovator Award for...
Alludo (Parallels), a global leader in cross-platform solutions, is excited to announce its recognition as a Major Player in two IDC MarketScape reports: the “IDC MarketScape: Worldwide Virtual...