
New report: Browsers are the front door to work and a prime target for attackers
Modern work depends on web-based access. Software-as-a-service (SaaS), internal web apps, partner portals, and GenAI tools are readily accessible for users, so browsers have become the most common workspace people use every day.
And if the browser is where people work, then it's also one of the most valuable entry points for attackers.
Recently, Omdia in collaboration with Parallels conducted research on browser management and security. They identified four key insights:
- Browser-based attacks are increasingly common, a growing cause for concern, and more accessible for malicious actors
- Unmanaged access is more common than you might think
- Organizations want solutions that layer into existing controls, rather than forcing replacements
- Budgets are shifting to match
Let’s take a closer look at these insights and what they mean for organizations.
Looking for a way to protect your organization’s browser-based access? Try Parallels Browser Isolation for free today.
Insight 1: Browser-based attacks comprise a substantial amount of incidents
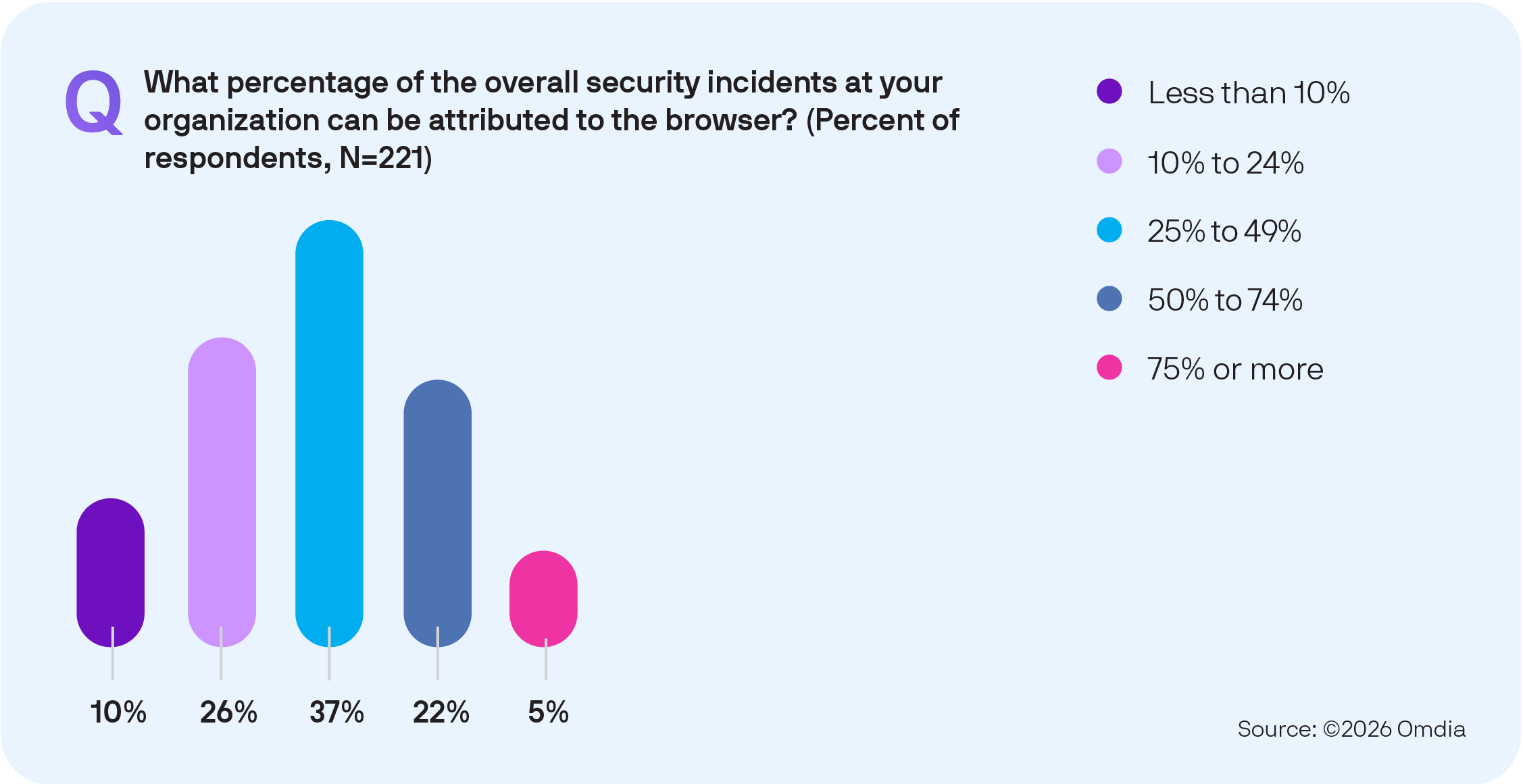
Among organizations that have experienced browser-based attacks in the last two years, respondents indicated that those incidents account for roughly 37% of their security incidents on average.
That’s not a rounding error.
It suggests that the browser isn’t just one more channel for threats anymore. It’s a primary avenue for bad actors to reach users.
Why attackers target browsers
Browsers typically contain three valuable types of information for attackers
- Identity: Browser sessions contain authentication states, tokens, and single sign-on (SSO) flows. Compromising a session can be as advantageous for a hacker as compromising an endpoint
- Data: Sensitive data increasingly lives in SaaS apps accessed through browsers
- User behavior: Browsing is fluid and fast. Users click links, open tabs, authenticate, and share content continuously, creating abundant opportunities for social engineering and deception
Why these attacks affect response and recovery economics
The research done by Omdia and Parallels showed that the downstream impacts of browser attacks go beyond security team time. Common outcomes from these attacks include downtime, compliance and legal work, and unplanned tool purchases.
These are organization-wide costs, not just security operations center (SOC) metrics.
When browser-based incidents happen frequently, the operational tax adds up in the form of more investigations, more user disruption, and more urgent decisions to stop the bleeding that can create longer-term complexity.
What mature browser security posture looks like
A mature approach to browser security should acknowledge that browsers are active execution environments, not passive viewers. Organizations should look to:
- Reduce the ability of web content to reach endpoints and internal networks
- Limit credential and session exposure
- Increase consistency of policy enforcement across different browsers and devices
- Design controls so the secure path is the easiest path for users
Insight 2: Unmanaged access is the rule, not the exception
On average, respondents reported that 32% of users access apps through unmanaged devices.
That’s a structural reality for many businesses. Contractors, third parties, bring-your-own-device (BYOD) users, frontline roles, and transitional IT phases, including M&A, all need access without full device control.

Why unmanaged devices break traditional assumptions
Security programs often assume you can:
- Enforce patching and configuration baselines
- Deploy agents and collect telemetry
- Standardize browsers, extensions, and update processes
- Rely on endpoint protections to contain threats
Unmanaged access challenges each assumption.
Even when a user is legitimate, the device may not be.
Browser versions lag, extensions vary, local storage behaviors differ, and controls are inconsistent.
How to pivot to securing sessions and data paths
When the device can’t necessarily be trusted, strategies need to focus on:
- Session-centric controls to contain risks at the point of access, namely the browsing session, rather than depending on endpoint posture
- Data-path controls to manage how content enters and leaves the session, including download, upload, clipboard, printing, keyboard access, and other exfiltration channels
- Tiered policies to apply stricter controls to higher-risk destinations like unknown sites, GenAI, file sharing, and sensitive SaaS while keeping lower-risk browsing smooth, ultimately leading to a Zero Trust approach that allows access only to explicitly approved sites
Why secure sessions and paths matter for user experience
A common path to failure for browser security mode is Shadow IT, the workarounds that users take—methods like emailing files to themselves, using personal devices, or shifting to unsanctioned tools.
The reality of unmanaged devices, even on protected networks and with sensitive files, makes usability a priority. User experience matters more than raw performance, and users need quick access that doesn’t require them to stop and evaluate their device, location, or the app they’re using.
Insight 3: Organizations want additive security, not a disruptive replacement
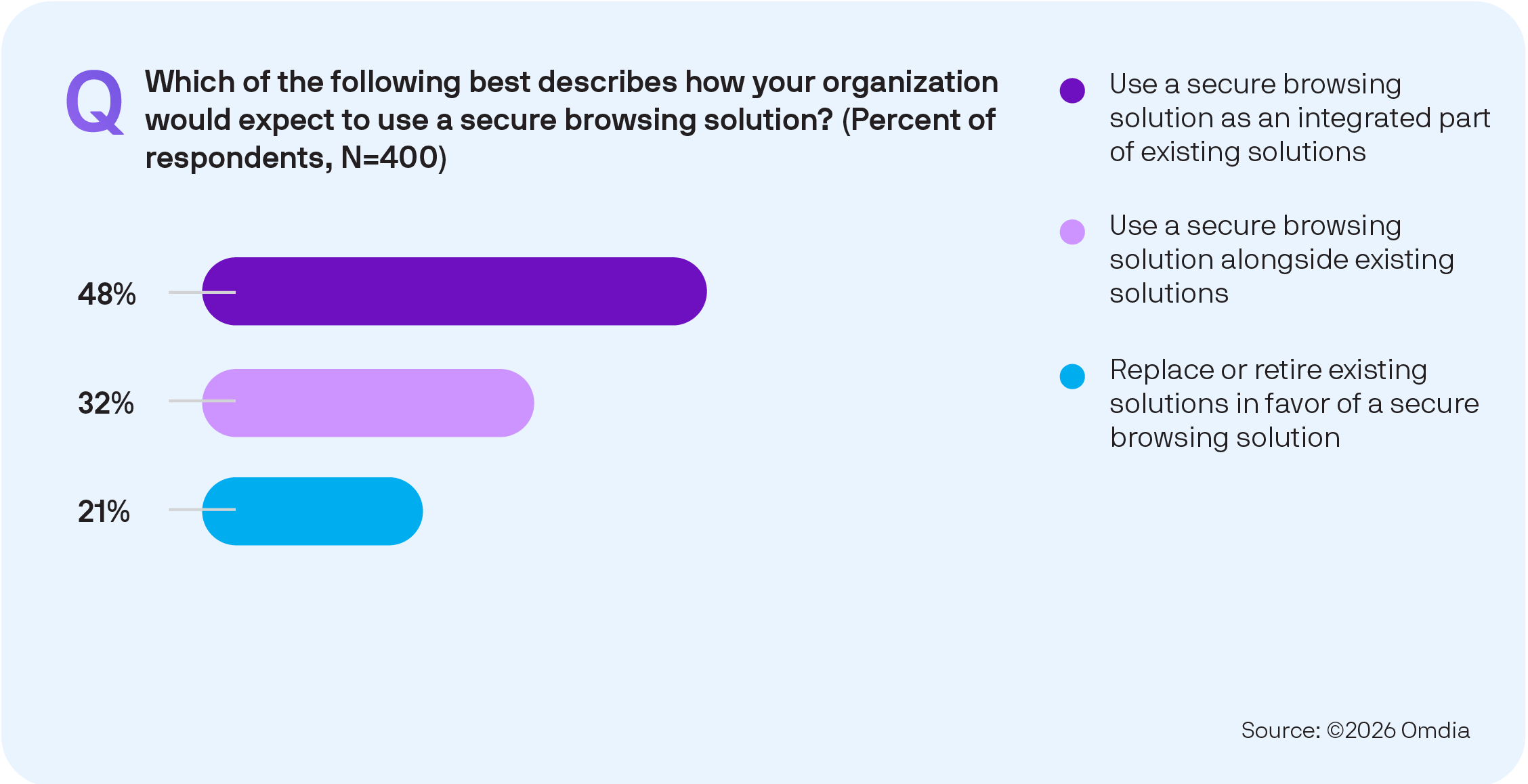
Only one in five respondents anticipated that secure browsing solutions will be deployed to replace or retire existing tools.
This shows how buyers think: Security stacks are already layered, and most teams want to improve outcomes without forcing a platform reset.
Why replacements are hard in the browser layer
Browser security isn’t limited to just one target. It touches:
- Identity and access management, including SSO and conditional access
- SOC workflows and visibility
- Endpoint management and posture
- App delivery methods like VDI, DaaS, and web apps
- Data protection programs like DLP and governance
Any solution that demands wholesale change risks long deployment timelines, inconsistent adoption, and user backlash.
Integration and flexibility are the real buyer priorities
Respondents reported that among the most desired attributes for their security strategies were integration and flexibility, including the ability to use existing browsers.
This makes sense. Browser standardization is harder than many teams admit. Chrome and Edge dominate, but Safari and Firefox still show up in formal and informal use, and many respondents simply don’t know the full extent of browser usage within their environment or on users' mobile devices.
In practical terms, buyers prioritize solutions that:
- Fit their current identity, device, and security tooling
- Reduce risk in targeted places first, including specific users, apps, or destinations
- Allow incremental expansion without forcing a single migration
Insight 4: Spending is moving toward secure browsing with clear expectations for value

The research indicates 85% of respondents expect secure browsing spend to increase, and respondents estimate a meaningful share of security budgets already allocated to this area.
The browser is now important enough to justify dedicated investment.
What’s inspiring budget momentum
A few forces reinforce one another:
- Browser-based incidents are taking a meaningful share of the overall workload
- Increased dependence on SaaS and web apps, where sensitive data is created and stored
- Expanding GenAI usage, often with unclear policy enforcement in practice
- A workforce reality that includes unmanaged endpoints and third-party access
Why spend depends on outcomes, not features
Many security categories have reached feature parity from a buyer’s perspective. What differentiates investment decisions is whether teams can demonstrate outcomes like:
- Reduced incident volume or reduced severity of web-borne threats
- Less time spent on investigations tied to browsing events
- Fewer policy violations or data leakage paths in sensitive workflows
- Faster enablement of contractors and partners without extending the endpoint footprint
- Improved consistency of access controls across devices and user populations
Cross-functional ownership has hidden impacts
The research notes strong collaboration between IT ops and security in secure browsing decisions. That’s important because adoption succeeds when:
- Security gets measurable risk reduction and better enforcement
- IT ops get a manageable deployment, predictable user experience, and lower support burden
Solutions that improve security while also simplifying day-to-day operations tend to retain funding over time.
How Parallels Browser Isolation solves secure browser concerns for organizations
Parallels Browser Isolation targets the concerns and priorities organizations have for their secure browsing strategies. It’s designed to give users a session-centric approach to web and SaaS risk while reducing the friction that causes shadow IT behaviors.
- Reducing the impact of browser-based attacks: By isolating browsing activity away from the endpoint, organizations can limit how much web-borne threats can directly reach devices and internal environments
- Handling unmanaged access: Parallels Browser Isolation supports securing access for contractors, third parties, BYOD, and other unmanaged scenarios by enforcing controls at the session layer rather than relying solely on endpoint posture
- Layering into existing programs: The research suggests buyers want additive approaches. Parallels Browser Isolation complements existing identity, web security, and endpoint programs, deployed first to the highest-risk users, apps, or destinations
- Enabling secure private application access without VPN complexity: Parallels Browser Isolation (PBI) Private Access secures SaaS, internal web applications, and privately hosted applications using sandboxed containers deployed on-premises, providing an alternative to traditional VPN access while maintaining a balanced control-plane and data-plane model
- Supporting measurable value: As budgets increase but scrutiny remains, Parallels Browser Isolation can be evaluated through outcomes-focused pilots focused on incident reduction, policy enforcement for sensitive workflows, and faster enablement of unmanaged access use cases
If your organization is looking for a practical way to reduce browser risk without waiting for perfect endpoint control or a full browser standardization effort, browser isolation can be a strong option to evaluate, and Parallels Browser Isolation is designed for exactly that kind of incremental, real-world rollout.
Sign up now for a free trial to learn more about how Parallels Browser Isolation can safeguard your digital interactions. Don’t miss out on this opportunity to enhance your organization’s security and efficiency.









